
Welcome to Cyber Mike’s
Cybersecurity Homepage
Thank you for visiting my Cybersecurity vision.
Please feel free to contact me with any questions.
Cybersecurity Principles – CIA Triad+

Confidentiality
Prevent sensitive information from unauthorized access attempts.

Integrity
Maintain the consistency, accuracy and trustworthiness of data over its entire lifecycle.

Availability
Information should be consistently and readily accessible for authorized parties.

Training & Awareness
Educate employees about cybersecurity threats, risks and best practices.

Incident Response
Organized approach to addressing and managing the aftermath of a cyber event.
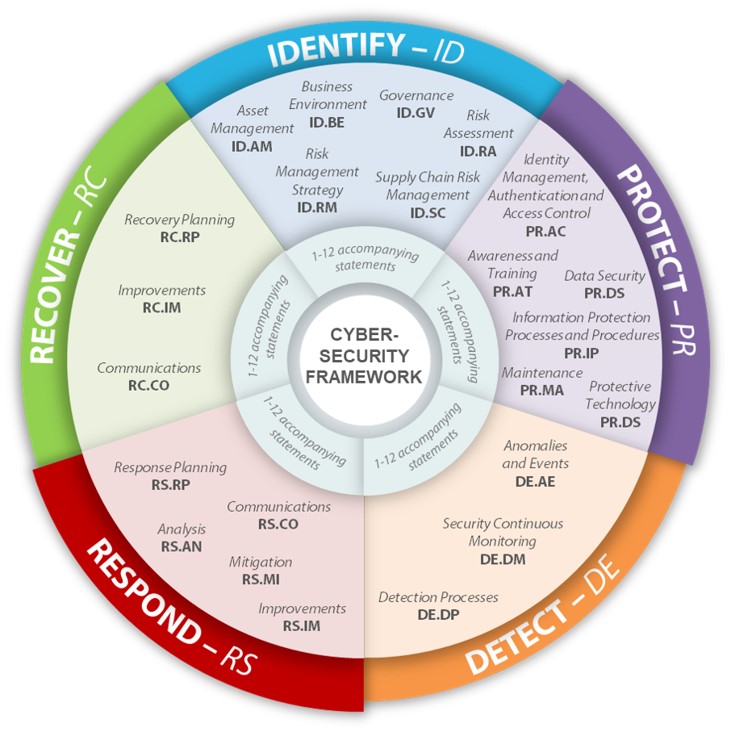
NIST Cybersecurity Framework
IDENTIFY
Develop the organizational understanding to manage cybersecurity risk to systems, assets, data, and capabilities.
PROTECT
Develop and implement the appropriate safeguards to ensure delivery of critical infrastructure services.
DETECT
Develop and implement the appropriate activities to identify the occurrence of a cybersecurity event.
RESPOND
Develop and implement the appropriate activities to take action regarding a detected cybersecurity event.
RECOVER
Develop and implement the appropriate activities to maintain plans for resilience and to restore any capabilities or services that were impaired due to a cybersecurity event.
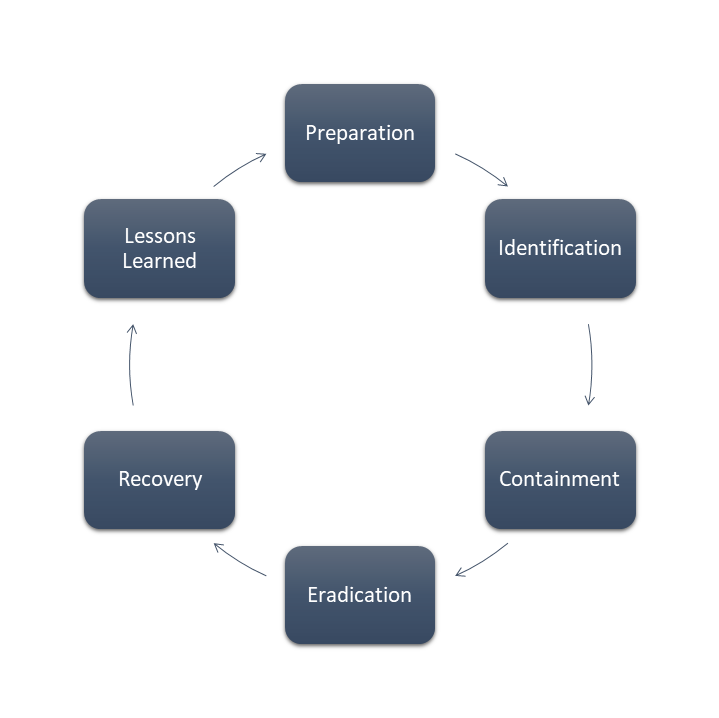
INCIDENT RESPONSE – PICERL
PREPARE
Fail to Prepare, Prepare to Fail. When not actively responding to an incident, you are in this phase. Strive to get better with continuous improvement and attack surface reduction. System hardening, vulnerability management, patching, monitoring, documentation, training and practice are some things you should focus on.
IDENTIFY
Something has happened, act quickly and accurately to assess the situation and properly determine if it really is in incident. Make sure to categorize the incident and prioritize the incident based on severity, risk and impact. Make sure to escalate if needed to ensure the proper incident responders are working any confirmed incidents.
CONTAIN
The goal here is to stop the attack from spreading. Do not rush into this to ensure there are no holes in your containment. You need to prevent things from getting worse by being decisive with your actions.
ERADICATE
Get the attacker completely out and keep them out in the future. This should be the more permanent fix that happens after the threat has been contained. Complete any hardening, patching and additional configuration required. Make sure to continue monitoring.
RECOVER
Restore affected systems back to their previous state with additional measures in place to ensure the incident or a similar incident cannot happen again. Test monitor and validate your systems as they are restored. Get things back to normal.
LESSONS LEARNED
Document and Learn. What happened in the incident? How did the incident happen? How was the incident dealt with? What went well with the incident response? What went bad with the incident response? What needs to be changed in the incident response plan?
DEFENSE IN DEPTH
PERIMETER SECURITY
Firewall, Penetration Testing, IDS/IPS, DDoS Protection
NETWORKING SECURITY
VPN, Wi-Fi Security, Secure DMZ, MDR, Continuous Monitoring
ENDPOINT SECURITY
NGAV/EDR, Asset Tracking, Rogue Device Monitoring, Patch Management, MFA, Endpoint Encryption
DATA SECURITY
PAM, MFA, Email Encryption, Data Backups, Database Monitoring, SIEM
BUSINESS OPERATIONS
Service Desk, SOC, Business Continuity, Disaster Recovery, Policies & Procedures, Governance, User Training, Vulnerability Management
PHYSICAL SECURITY
CCTV Security System, Access Control System, Guest Management, Alarm System, Power Backup, Fire Suppression

CYBERSECURITY MESH ARCHITECTURE
Securing our devices and data regardless of location, device or data state (at rest, in transit) by leveraging various technologies and processes (both automated and human-based processes).
Extending Cybersecurity controls everywhere needed by ensuring our platforms are scalable, flexible and resilient.
Standardizes our incident response, threat mitigation and event recovery strategy. (our responses become consistent, rehearsed and efficient).
